I have been using OSSEC for a while now but I always used only plain text logs. While this is not bad, it does not scale really well. I started looking into a way to do it right(tm). I knew OSSEC was compatible with MySQL, and since 2.7 has been released, it gave me an excuse to play with it again.
You will need to enable MySQL in OSSEC (not enabled by default), grab the source then do the following. Note that if upgrading an existing installation, you might want to save the registered client keys, the file to back up is: /var/ossec/etc/client.keys
cd ossec-hids-2.7/src make setdb cd .. ./install.sh
After you have completed the installation, you need to configure your MySQL server, I used the official documentation to do it. Here is my run down of it:
$ mysql -u root -p
mysql> create database ossec;
mysql> grant INSERT,SELECT,UPDATE,CREATE,DELETE,EXECUTE on ossec.* to ossecuser@<ossec ip>;
mysql> set password for ossecuser@<ossec ip>=PASSWORD('ossecpass');
mysql> flush privileges;
mysql> quit
mysql -u root -p ossec < ./src/os_dbd/mysql.schema
You just now need to edit /var/ossec/etc/ossec.conf and add a new section within the config:
<database_output>
<hostname>127.0.0.1</hostname>
<username>ossecuser</username>
<password>xxxxxxx</password>
<database>ossec</database>
<type>mysql</type>
</database_output>
And at last, enable MySQL and restart the service:
/var/ossec/bin/ossec-control enable database /var/ossec/bin/ossec-control restart
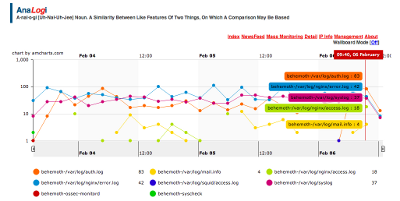
Analogi is a web interface replacement to ossec-wui which is now very dated and spurts too many false positive. To install analogi, go to the main project page and clone it using git:
git clone git://github.com/ECSC/analogi.git
It is up to you to protect that folder on your webserver as this has potential security risks, I am using NGINX, so here is my setup:
location /ossec/analogi {
auth_basic "Restricted Access";
auth_basic_user_file htpasswd-file;
}
You then need to rename the config file and change the SQL information
mv db_ossec.php.new db_ossec.php
You should now be able to see information gathered from different clients straight into MySQL and using Analogi.